

For C-Suites
ShapeShift ciphers comprise a family of evolutionary, amorphous, military-grade, symmetric data encryption procedures that utilize customizable ensembles of obfuscation techniques. Through Quantum Superpositioning emulation and well-known standard principles, instantiations provide unsurpassed data encryption strength and unsurpassed performance.
Unlike traditional and newly emerging Post Quantum Cryptography methods that rely on complex, esoteric mathematical foundations, ShapeShift ciphers has a simple, discreet Deterministic Chaos foundation that avoids mathematical complexity. This allows ShapeShift ciphers to produce mathematically barren plateau ciphertexts that naturally neutralize unauthorized Quantum and classical computer decryption attempts on first principles. Specifically, while mathematical foundations enable cryptographers to construct difficult-to-solve challenges, Deterministic Chaos foundations enable cryptographers to construct unsolvable challenges that have no patternicity or solution.
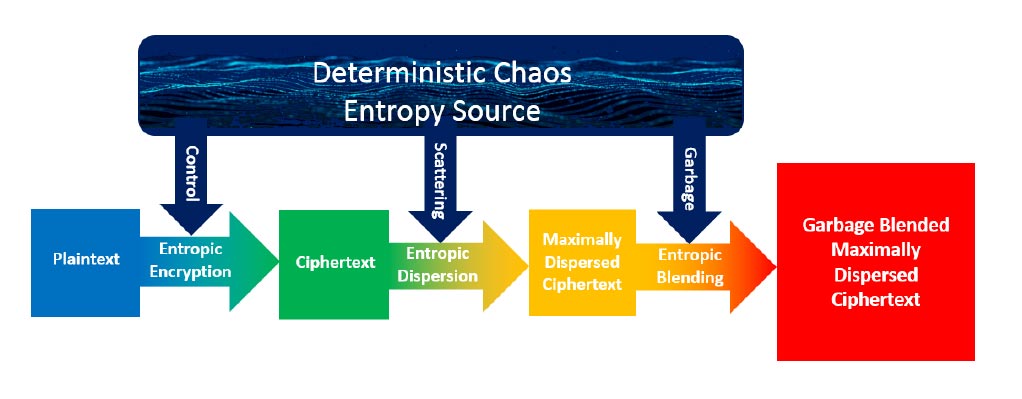
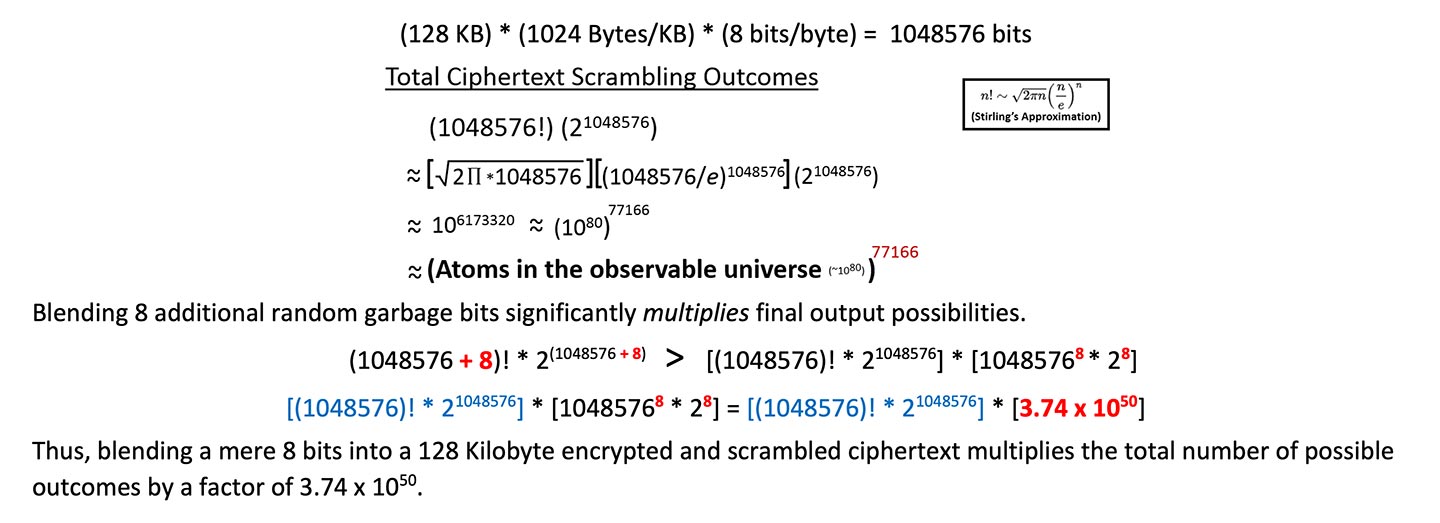
Extremely simple, atomic, bijective, invertible operations provide unsurpassed encryption and decryption performance under the direction of a dynamically constructed, discreet Deterministic Chaos Entropy Source. A complete encryption process typically involves three processes, collectively referred to as ShapeShift Triplex™ Entropy Infusion. Each process references the Deterministic Chaos Entropy Source to affect different purposes. (Read more...)
For C-Suites